
Overview of the Security Threat
Recently, cybercriminals have begun exploiting a serious authentication bypass vulnerability in CrushFTP file transfer software. This security breach leverages publicly available proof-of-concept exploit code, posing a severe threat to data security.
Details on the Vulnerability (CVE-2025-2825)
The flaw, identified as CVE-2025-2825, was initially reported by cybersecurity firm Outpost24. It impacts CrushFTP versions 10 and 11 and permits remote attackers to access systems without authentication. Owners of the affected software versions were advised to patch their systems following a security alert and update release from CrushFTP.
Temporary Security Measures
For users unable to immediately deploy the necessary updates, enabling the DMZ (demilitarized zone) perimeter network option is recommended as an interim safeguard until the updates can be applied.
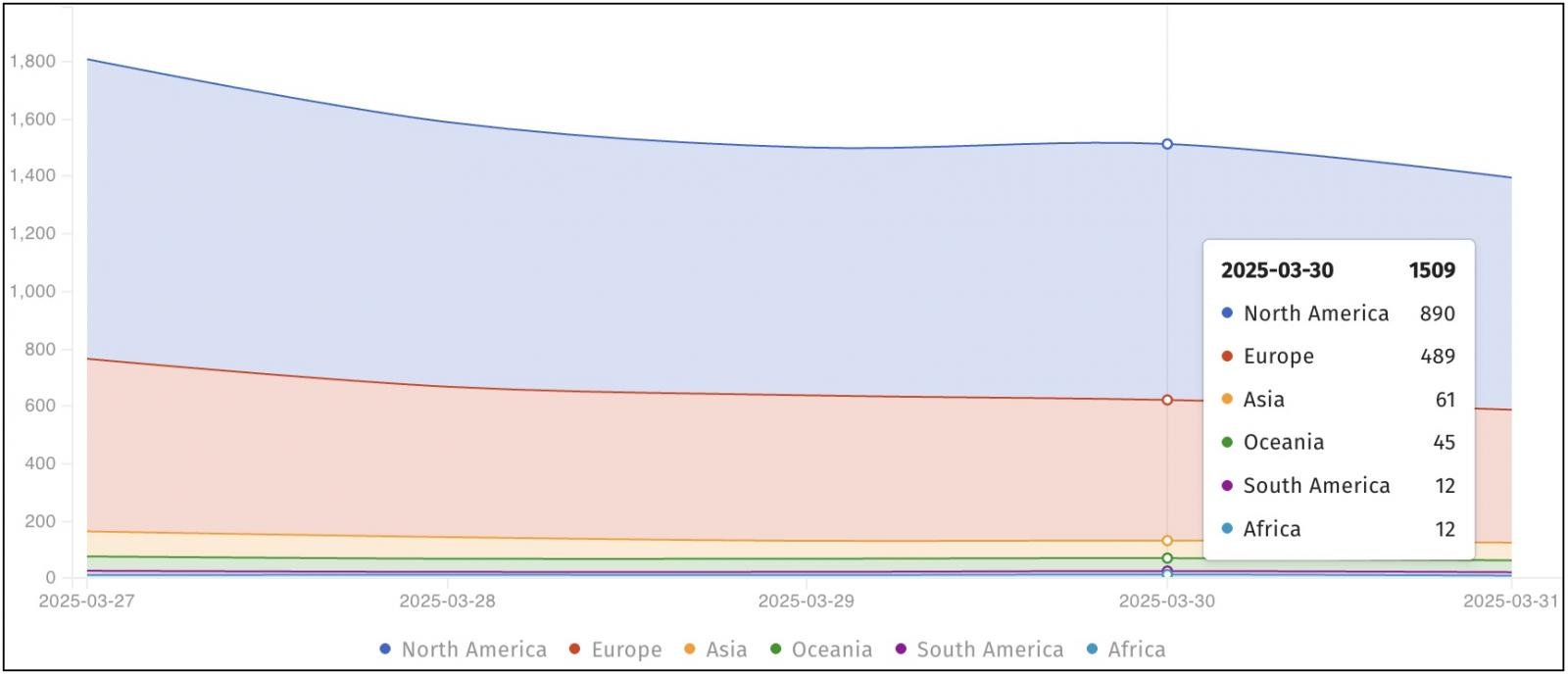
Current Exploitation Status
One week after the vulnerability report, security monitoring organization Shadowserver detected numerous exploitation attempts on CrushFTP servers openly accessible on the internet, affecting over 1,500 instances. This warning closely followed a detailed publication by ProjectDiscovery regarding the technical specifics and exploitation methods of CVE-2025-2825.
Related Security Incidents
In the past, CrushFTP has been targeted by numerous ransomware groups, notably by Clop, due to its vulnerabilities. Other file transfer products have also been under threat, marking a growing trend in targeting essential data transfer infrastructures.
Historical Vulnerabilities and Responses
Previously, CrushFTP addressed a similar critical issue, a zero-day vulnerability in April 2024, identified as CVE-2024-4040, which allowed attackers to bypass virtual file system security. This incident led to significant security responses from entities like CISA, emphasizing the urgency in patching the vulnerabilities.
Call to Action
CrushFTP users are urged to update their systems immediately to prevent potential breaches. Given the gravity of the threat landscape, maintaining robust security measures and quick response to vulnerabilities is paramount for safeguarding critical IT infrastructure.
Related: 30 Essential Penetration Testing Tools for Enhanced Cybersecurity
Last Updated: April 1, 2025