
Understanding Lucid’s Global Impact
A sophisticated phishing-as-a-service (PhaaS) operation known as Lucid is currently targeting 169 entities across 88 countries through meticulously crafted messages delivered via iMessage for iOS and RCS for Android.
This nefarious platform, managed by a group of Chinese cybercriminals dubbed the XinXin group, offers its malicious services on a subscription basis. It provides customers—including various threat actors—with over 1,000 phishing domains, bespoke auto-generated phishing sites, and top-tier spamming tools.
Insights from Prodaft researchers highlight a link between Lucid and another PhaaS platform, Darcula v3, suggesting a collaborative or interconnected operation.
Lucid’s Subscription and Operations
Lucid’s subscriptions are marketed through a dedicated Telegram channel, gathering more than 2,000 members. Users can acquire access through weekly licenses, enhancing flexibility for ongoing criminal campaigns.
Maximized Messaging with Secure Technologies
Every day, Lucid claims to dispatch over 100,000 smishing messages leveraging the end-to-end encryption facets of RCS and Apple iMessage. This method effectively allows them to bypass conventional spam filters, thus heightening the operation’s success rate.
The platform’s key strategy includes:
- Automated attack delivery systems deploying customizable phishing websites primarily via SMS.
- Utilizing Apple iMessage and Android’s RCS functions to sidestep traditional SMS spam filters, significantly boosting delivery and success metrics.
- Cost-effectiveness, as using these messaging services reduces operational costs compared to traditional SMS.
Tactical Deployment and Operation Security
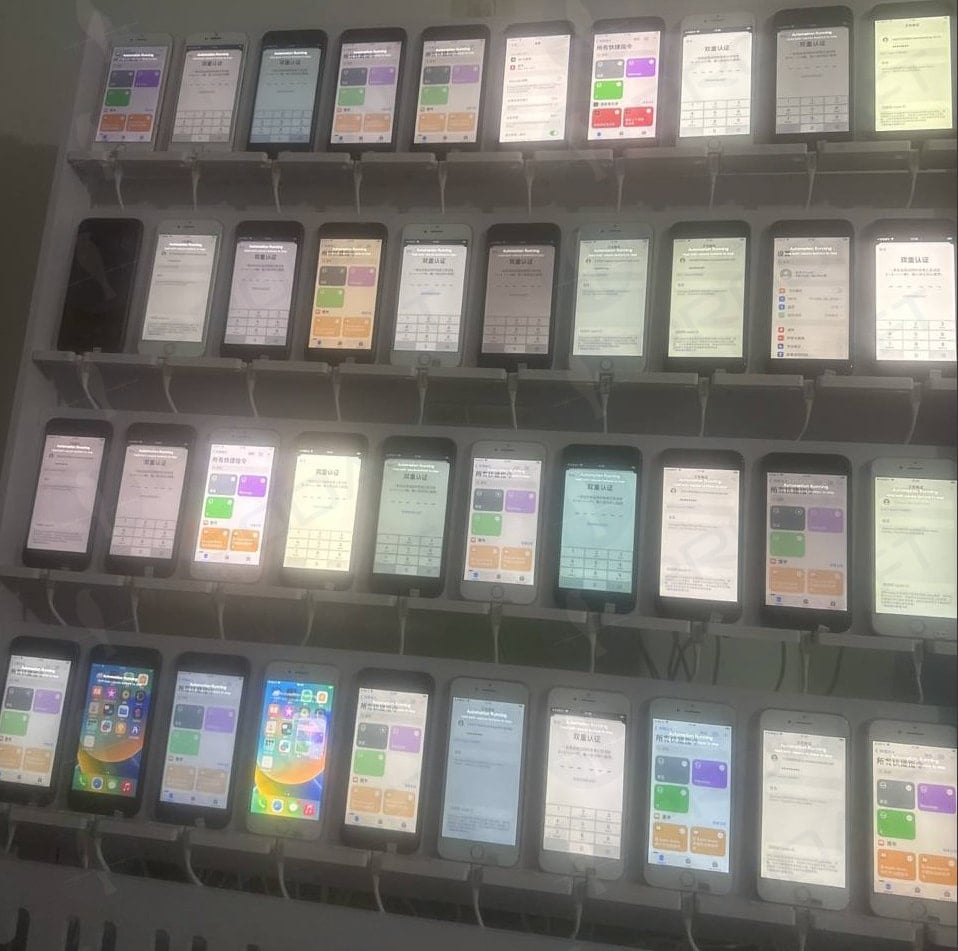
To execute their strategy, operators at Lucid manage large-scale iOS and Android device farms. Specific tactics include using temporary Apple IDs for iMessage and exploiting flaws in carrier implementations of RCS, allowing unauthorized sender validations.
A video shared by Prodaft reveals the threat actors conducting phishing operations from moving vehicles, likely to increase operational security and evade detection by law enforcement and mobile carriers.
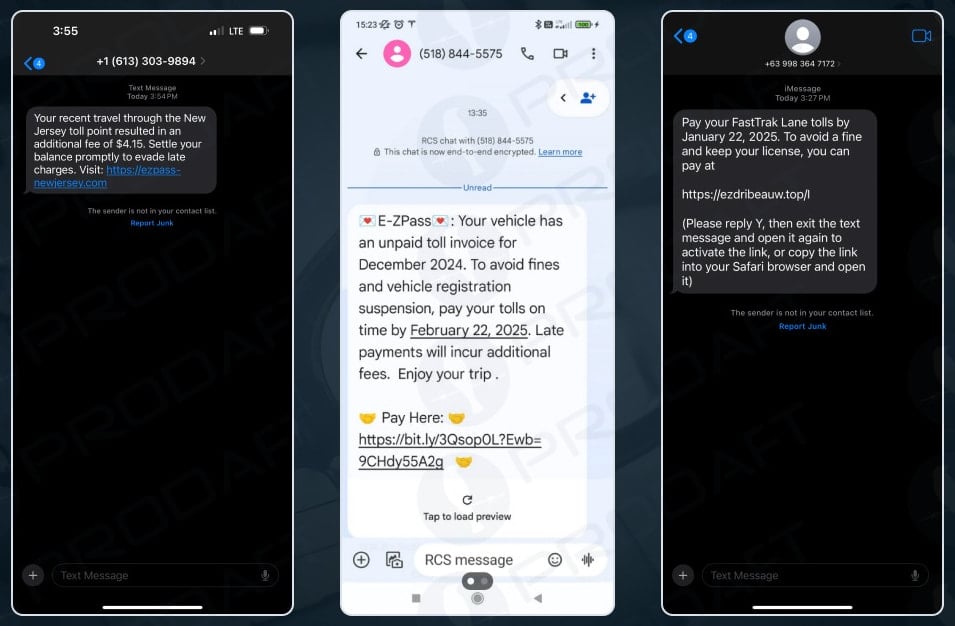
The content of mobile phishing messages often mimics alerts related to shipping, tax notifications, or missed toll payments and employs:
- Custom logos and branding adapted to the target demographic.
- Geo-location filtering to target the victims more precisely.
Victim Impact and Safety Steps
Clicking on the phishing links directs victims to fraudulent pages posing as various legitimate entities such as USPS, DHL, and major banks, aimed at stealing sensitive personal and financial information.
The platform’s built-in credit card validator allows criminals to immediately test the validity of stolen card details for subsequent fraud or resale.
To safeguard against such threats, it is crucial to ignore unsolicited messages urging link clicks or replies. Verify any potential alerts or needed actions by directly logging into the official services instead.
Related: Lazarus Group is No Longer Consider a Single APT Group, But Collection of Many Sub Groups
Last Updated: March 31, 2025




