Introduction
The Acronis Threat Research Unit (TRU) recently conducted an in-depth analysis of a formidable malware delivery chain and uncovered some ingenious strategies used to target and deceive victims. This article explores the multifaceted stages of the infection, shedding light on the tactics employed by cybercriminals to deploy notorious malware variants such as DCRat and Rhadamanthys.
Detailed Analysis of the Initial Infection
The Deceptive Email Strategy
It all starts with an email designed to alarm: a RAR file named “Citación por embargo de cuenta” or “Summons for account garnishment.” This tactic specifically targets Spanish-speaking individuals, prompting them to open the attachment out of concern. Once extracted, the RAR file reveals a Visual Basic Script (VBS) that kicks off the malware’s multi-stage infection process.
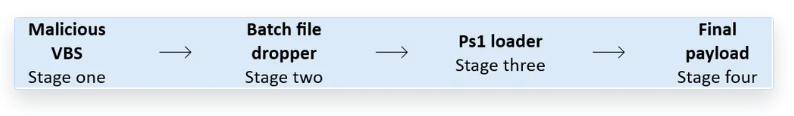
Exploring the Multi-Stage Delivery Process
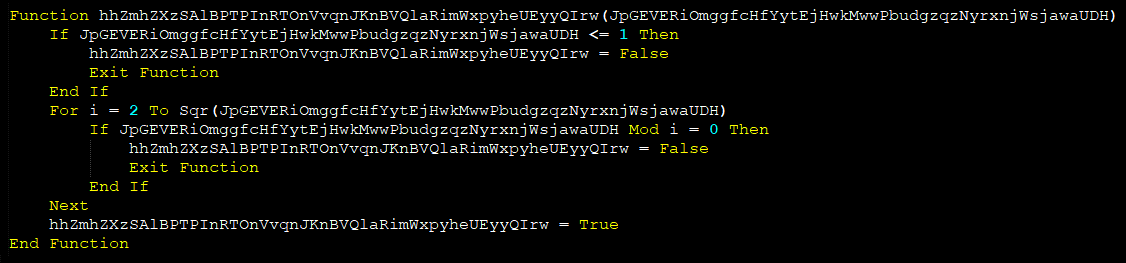
This section discusses the layers of the delivery mechanism, which begin with the aforementioned VBS file. This script is heavily obfuscated, which complicates detection by conventional security solutions.
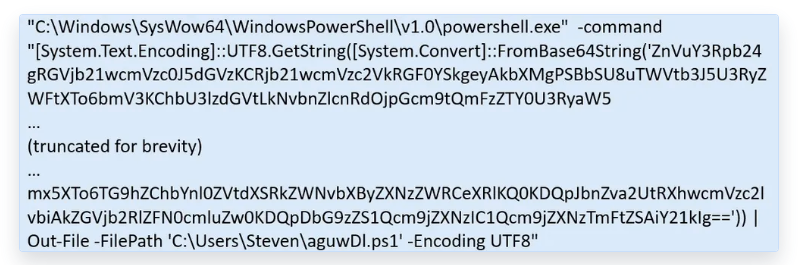
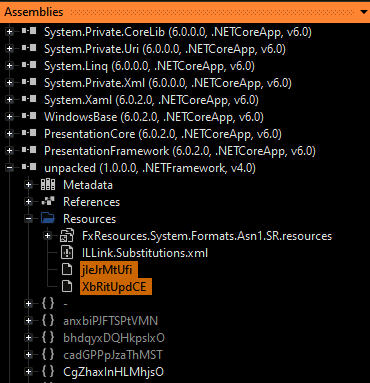
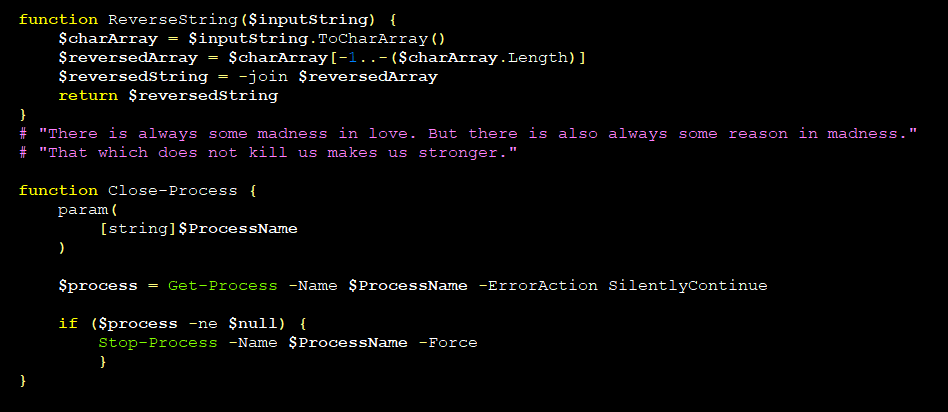
Subsequently, the script crafts a Windows batch file. This file creates a Base64 encoded PowerShell script, which executes and decodes to unleash the malware payload—a Windows .NET executable. This executable, packed with sophisticated obfuscation techniques including encrypted data blobs, poses extremely high risks.
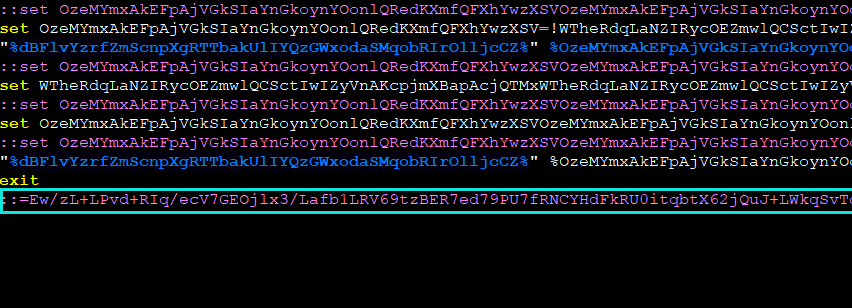
Complex Obfuscation and Evasion Techniques
The malware employs multi-layered obfuscation and various script languages to infect systems. This complexity not only helps evade detection but also makes it challenging for security solutions to contend with each infection phase.
Multilayered Defense: The Necessity of Advanced Security Solutions
Fighting such advanced threats mandates the deployment of robust, multilayered security strategies. These include:
- Early detection and blocking of malicious emails and attachments.
- Employment of advanced heuristics and behavior analysis to detect suspicious script activities.
- Real-time protection capabilities to halt encoded payloads from executing.
The Acronis Advanced Security + Extended Detection and Response (XDR) exemplifies such a comprehensive defense, providing critical, early-stage threat detection and neutralization.
Key Findings and Unexpected Philosophical Insights
During the de-obfuscation process, the TRU team unearthed surprising elements like quotations from Friedrich Nietzsche embedded within the PowerShell script, demonstrating the malware authors’ creativity and deep cultural knowledge. This aspect also highlights an additional method used by attackers to distract and confuse analysts.
Conclusion and Further Information
The detailed examination by the Acronis Threat Research Unit reveals the elaborate and sophisticated nature of modern malware deployment tactics. Stakeholders are encouraged to examine the full technical write-up and stay updated via the Acronis research blog.
This analysis serves as a reminder of the ever-evolving threat landscape and underscores the importance of advanced, adaptive security defenses in protecting against sophisticated cyber attacks.
Related: Apple Faces €150 Million Fine for Controversial App Tracking Practices
Last Updated: April 1, 2025




