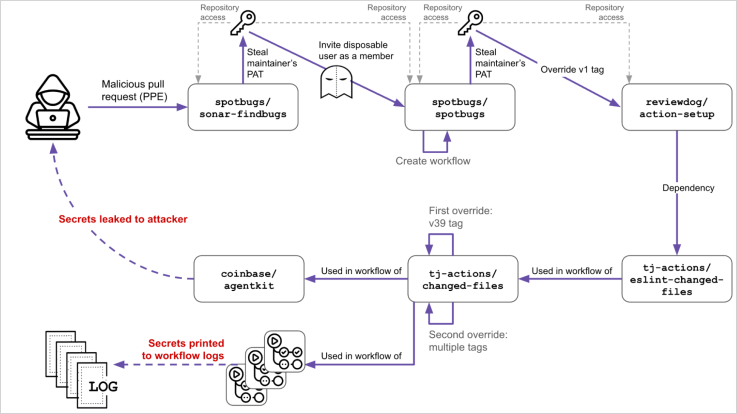

Overview of the Incident
The recent attack on GitHub, which specifically targeted projects tied to Coinbase, has been traced to a compromised token from a SpotBugs workflow. This theft enabled attackers to impact several GitHub projects, escalating to a comprehensive supply chain compromise.
The Breach Explained
In November 2024, a breach involving SpotBugs, a widely used static analysis tool, brought about unexpected vulnerabilities. This led to the compromise of Reviewdog, causing a domino effect that subsequently impacted tj-actions/changed-files.
Detailed Breakdown of the Attack
The multi-step attack compromised secrets across 218 repositories. New evidence suggests that the initial focus was on cryptocurrency exchange projects, specifically Coinbase, marking a deliberate attempt to infiltrate high-value targets.
Palo Alto Networks’ Unit 42 unearthed the origins of this incident, revealing that the invasion began with the unintentional inclusion of a Personal Access Token (PAT) in a CI workflow by a SpotBugs maintainer, identified only as SPTBHS_MNTNR.
The Cascade Commences
By exploiting a vulnerable ‘pull_request_target’ workflow, an attacker stole the maintainer’s PAT through a deceptive pull request in early December 2024.
Several months later, using this stolen PAT, the attacker facilitated further breaches by inviting an accomplice to inject malicious GitHub Actions workflows that siphoned additional tokens and inflicted more extensive damage.
Illustration of the Attack
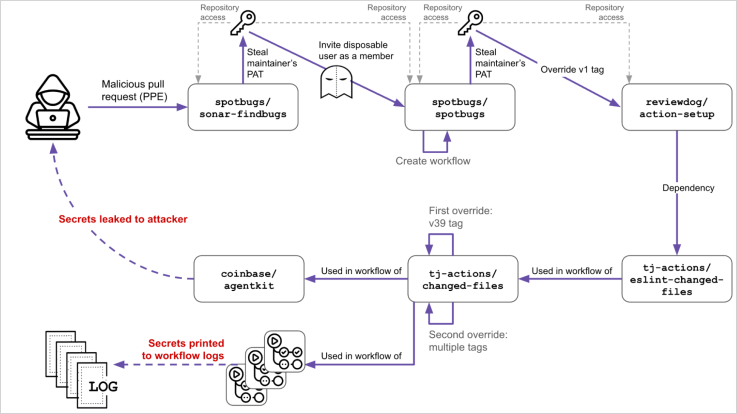
Source: Unit 42
Impact and Implications
Although the attacker aimed to extract secrets from Coinbase’s infrastructure, their efforts were foiled as the compromised workflow was detected and deactivated in time.
This incident sheds light on critical vulnerabilities within the GitHub Action ecosystem, highlighting the need for better audit logs and stricter controls over tag mutability.
Recommendations for Enhanced Security
- Immediate rotation of all secrets in projects using the tainted actions.
- Thorough audit of GitHub Actions logs, especially those within the attack timeframe, to identify any unauthorized data exposure.
- Use of commit hashes instead of tags to pin dependencies to safeguard against similar vulnerabilities.
- Prudent limitation of the ‘pull_request_target’ feature to cases where it is unequivocally required.

Dive deeper into the tactics and prevention methods outlined in the Red Report 2025, summarizing the analysis of 14 million malicious actions.
Read the Red Report 2025
Related: Cyberattack Paralyzes Minnesota Tribal Community: Comprehensive Breakdown
Last Updated: April 3, 2025