
Introduction
Oracle, a heavyweight in the cloud computing arena, has recently come forward to inform certain clients about a significant security lapse. Attackers managed to pilfer outdated customer credentials from a legacy platform last active in 2017, raising serious questions about data integrity and security measures.
Details of the Security Breach
Despite reassurances from Oracle categorizing the compromised data as non-sensitive legacy information, investigative reports and data shared with BleepingComputer suggest a more alarming scenario with newer records from as recently as 2025 leaked online. The revelation has spurred an investigation by cybersecurity powerhouse CrowdStrike along with the FBI to dig deeper into this disturbing incident.
Exploit and Data Exfiltration
Cybersecurity specialist CybelAngel has uncovered that the breach stemmed from an old vulnerability in Java, exploited by hackers as early as January 2025. The intruders installed a web shell and additional malware on Oracle’s initial generation servers, popularly known as Oracle Cloud Classic. The breach, which was detected by the end of February 2025, led to the theft of vital data from Oracle Identity Manager (IDM) databases comprising user emails, hashed passwords, and usernames.
Marketplace Data Sale and Oracle’s Defense
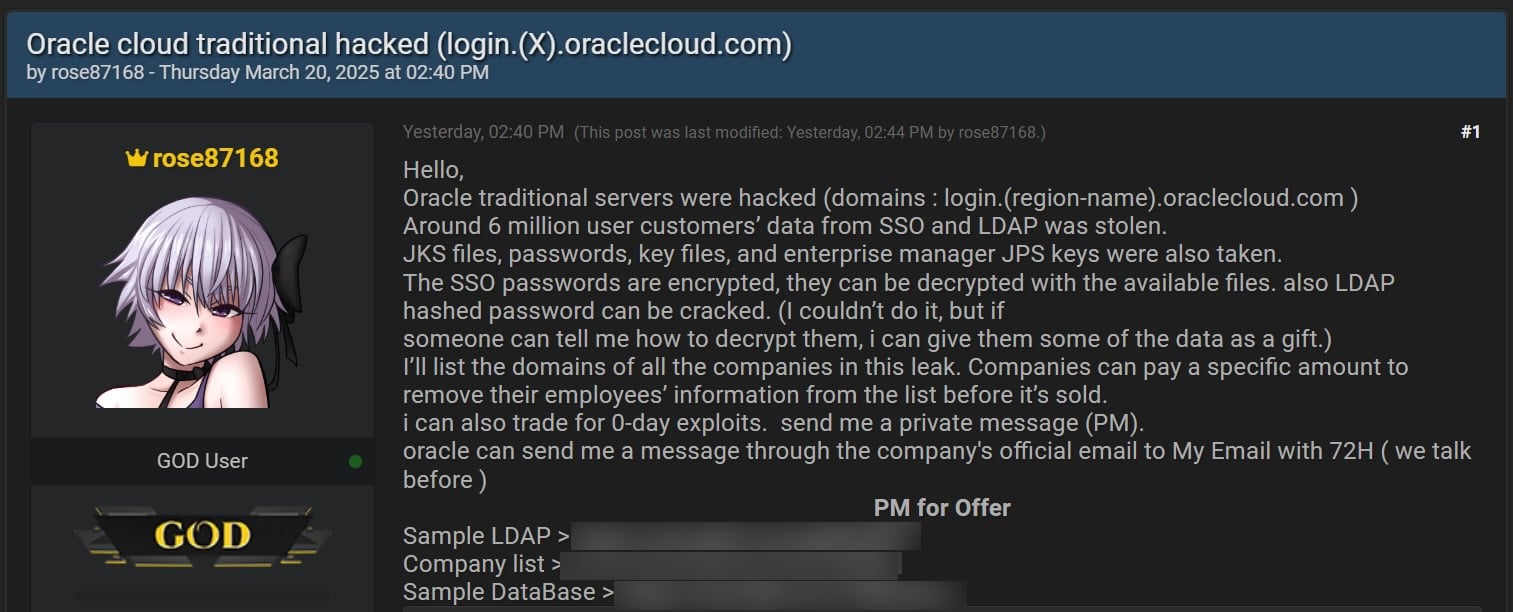
A nefarious threat actor identified as rose87168 exacerbating the issue further, trafficked around 6 million Oracle data records on notorious cyber-underworld forums in March. Oracle, in response to these daunting disclosures, strongly refuted claims of any breach involving Oracle Cloud, asserting that the leaked credentials did not pertain to its current cloud services.
Additional Incidents and Oracle’s Crisis Management
The saga doesn’t end there. Oracle was also embroiled in a data breach at its SaaS entity, Oracle Health, affecting several U.S. healthcare providers. While Oracle detected the breach on Oracle Health’s legacy data migration servers in late February, details gleaned from quiet communications with affected clients reveal sensitive patient data was compromised.
User Verification and Pending Disclosure
BleepingComputer has verified the legitimacy of the leaked data samples including associated LDAP display names and emails through multiple confirmations with affected companies, yet Oracle continues to decline any security failure at its cloud facilities, citing the incidents implicated the older Oracle Cloud Classic.
Oracle’s Controversial Statements and Public Reactions
Critics, including cybersecurity expert Kevin Beaumont, accuse Oracle of semantic play by renaming its old cloud services to Oracle Classic in an effort to muddle the truth about the breaches. This stratagem, however, has been only partially successful as continued scrunity and analysis unmask the severity and extent of the security mishaps.
Conclusion
Oracle’s handling of the breach disclosures is under close observation by regulatory bodies and cybersecurity communities. Trust and transparency remain pivotal as Oracle navigates through these turbulent waters, endeavoring to fortify its systems and restore client confidence in its cloud ecosystems.
Related: Unraveling the GitHub Supply Chain Breach: How a Leaked Token Led to a Multi-Project
Last Updated: April 3, 2025