
**Meta Description: Uncover how 46 newly discovered security vulnerabilities in top solar inverters pose severe risks to power grids and user privacy.**
Overview of Solar Inverter Vulnerabilities
The discovery of 46 critical security flaws in solar inverters from industry leaders Sungrow, Growatt, and SMA could potentially enable malicious actors to control these devices or execute unauthorized code on associated cloud platforms. This raises significant concerns about grid stability and user privacy. The vulnerabilities, discovered by cybersecurity experts at Vedere Labs, have been deemed severe due to their potential to disrupt or even damage power grids by creating an imbalance in power generation and demand.
The Risk of Inverter Hijacking
Vedere Labs have identified various ways in which the vulnerabilities could be exploited:
- Unauthorized cloud platform access
- Remote code execution
- Device takeover
Specifically, one vulnerability (CVE-2025-0731) affects SMA products and could enable remote code execution through the uploading of .ASPX files.
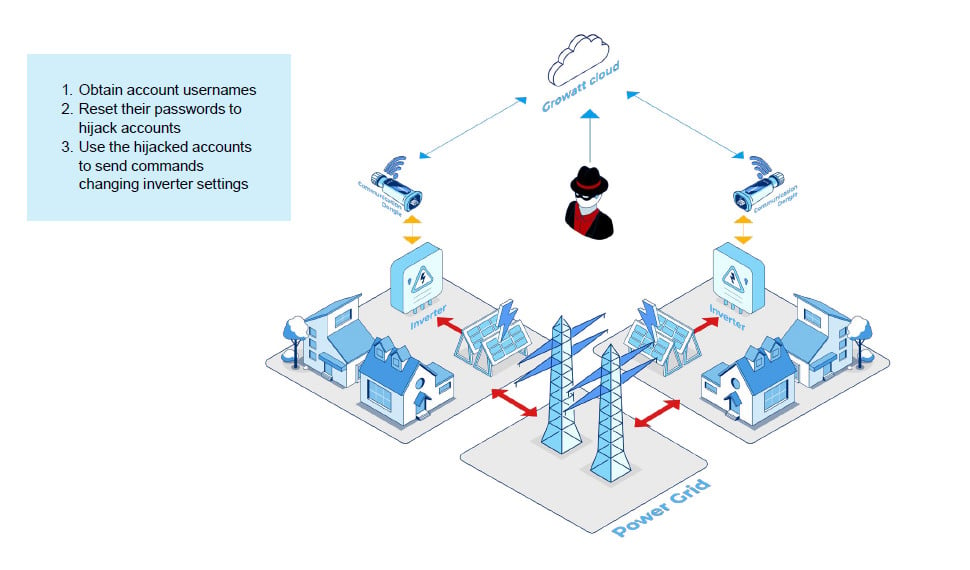
The report also outlines scenarios where Growatt and Sungrow inverters can be hijacked, with easier access through cloud backends in the case of Growatt inverters.
Exploitation Tactics and Impacts
The attack strategies include:
- Harvesting communication dongle serial numbers through various vulnerabilities.
- Using hardcoded MQTT credentials to manipulate inverter functions.
- Executing code remotely on communication dongles to take complete control of the devices.
This comprehensive control could lead to a coordinated attack on power grids, especially during peak production times, by inversely modulating the power generation of the hacked inverters.
Additional Risks and Vendor Responses
Besides grid disruption, these vulnerabilities also pose a risk to user privacy and could potentially enable attacks on smart home devices or facilitate ransomware operations. Notably, both Sungrow and SMA have acted promptly to address these issues, with Growatt also deploying necessary patches.
For more in-depth technical details and recommendations, refer to the full report available from Forescout’s Vedere Labs. Protect your systems by staying informed about the latest security vulnerabilities.
Learn More and Stay Protected
Access a detailed report on these vulnerabilities and learn protection strategies by visiting Forescout’s detailed research.
Related: 5 Alarming Ways Atlantis AIO is Revolutionizing Credential Stuffing Attacks
Last Updated: March 27, 2025