
Overview of the Incident
The Call Filter feature by Verizon, a tool designed to enhance telephone security for its users, was recently found to contain a significant vulnerability. This loophole allowed unauthorized access to the incoming call history of other Verizon Wireless subscribers through unprotected API requests.
Discovery and Repair
Security expert Evan Connelly uncovered this breach on February 22, 2025. His findings, which were subsequently corrected by Verizon in the weeks following, shed light on the potential duration of the exposure, though complete details remain uncertain.
Functionality of Verizon’s Call Filter
Verizon offers its Call Filter service free of charge, providing essentials like spam detection and automatic call blocking. The optional premium service enhances capabilities with features such as spam look-up services and customized call blocking:
- Pre-installed on all eligible Android and iOS devices bought from Verizon
- Estimated to be actively used by millions
Technical Details of the Flaw
The security flaw was associated particularly with the API functionality of the Call Filter app. It specifically involved how the app processed authentication and access:
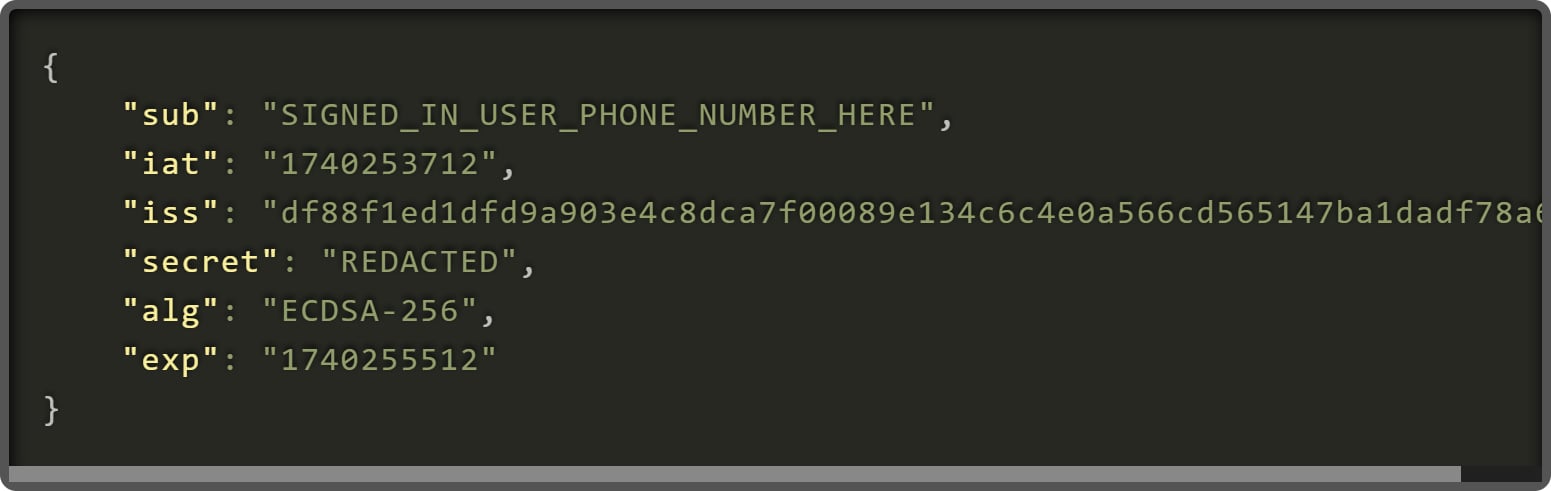
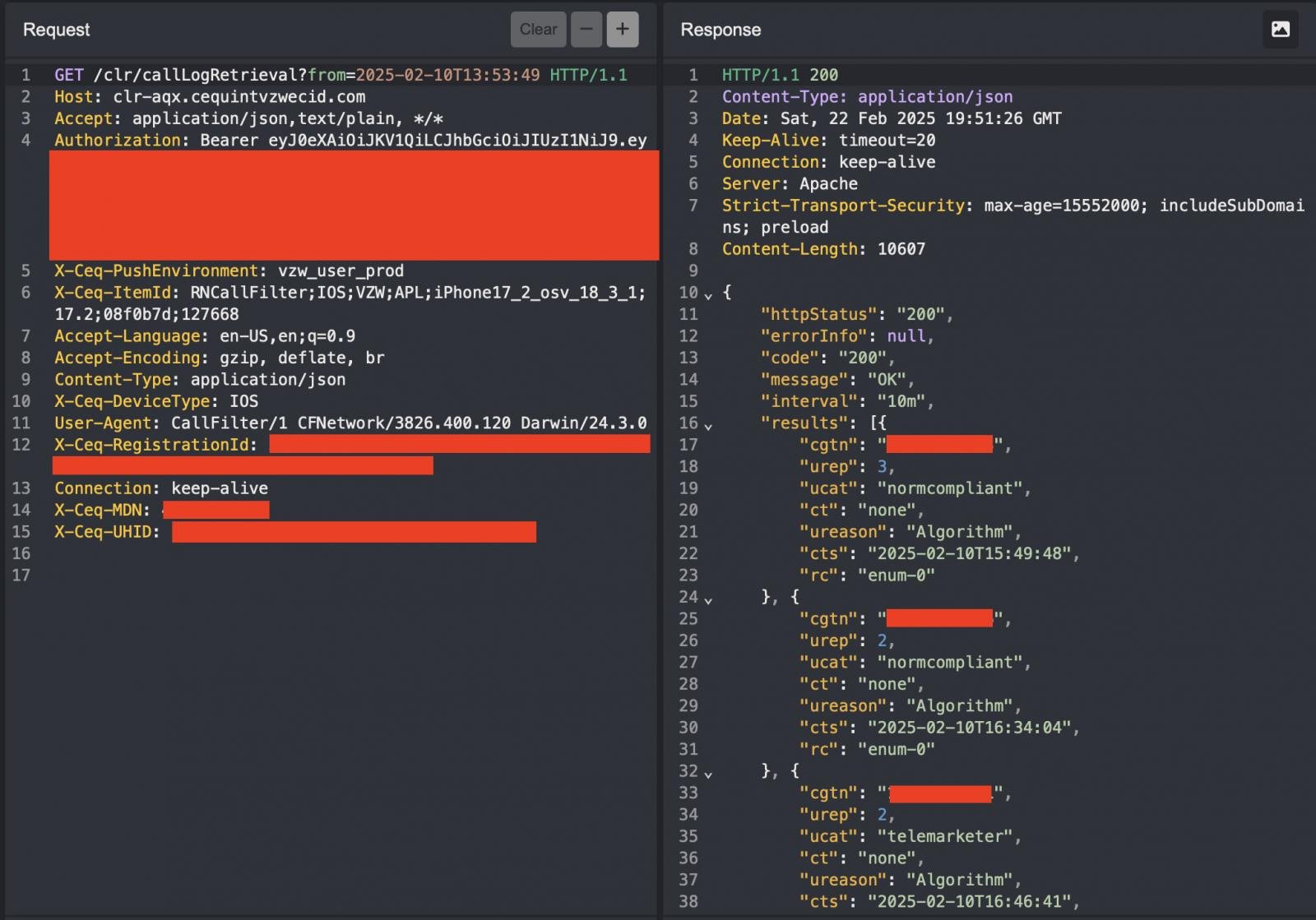
“This endpoint requires a JSON Web Token (JWT) and uses an X-Ceq-MDN header to specify a cell phone number for accessing call logs,” explained Connelly.
The exploitation was alarmingly straightforward. An attacker could simply manipulate the header value to fetch call logs other than their own, potentially leading to severe privacy breaches, especially among high-profile Verizon subscribers.
Call History Exposure Implications
By accessing call logs, malicious entities could:
- Track daily movements and routines
- Determine frequently contacted individuals
- Analyze personal and business relationships
This unethical access could transform a simple call history into a potent tool for surveillance.
Security Measures and Further Concerns
The API’s architecture—a third-party server managed by Cequint—was particularly troubling. Questions about Cequint’s operational security, given their currently nonfunctional website, added to the concerns surrounding the handling of sensitive call data.
Conclusion and Verizon’s Response
While Verizon acted swiftly to rectify the disclosed issue, the incident highlights the critical need for robust security frameworks in protecting user data. Ongoing inquiries into whether this vulnerability had been exploited or affected all Verizon Call Filter users remain unanswered.
Related: 5 Alarming Tactics Cybercriminals Use to Deploy Ransomware via Vishing and MS Tools
Last Updated: April 2, 2025




