
Overview
North Korean IT professionals, often called “IT warriors”, are accelerating their undercover operations within European organizations, leveraging deception to appear as local workers to secure remote IT roles.
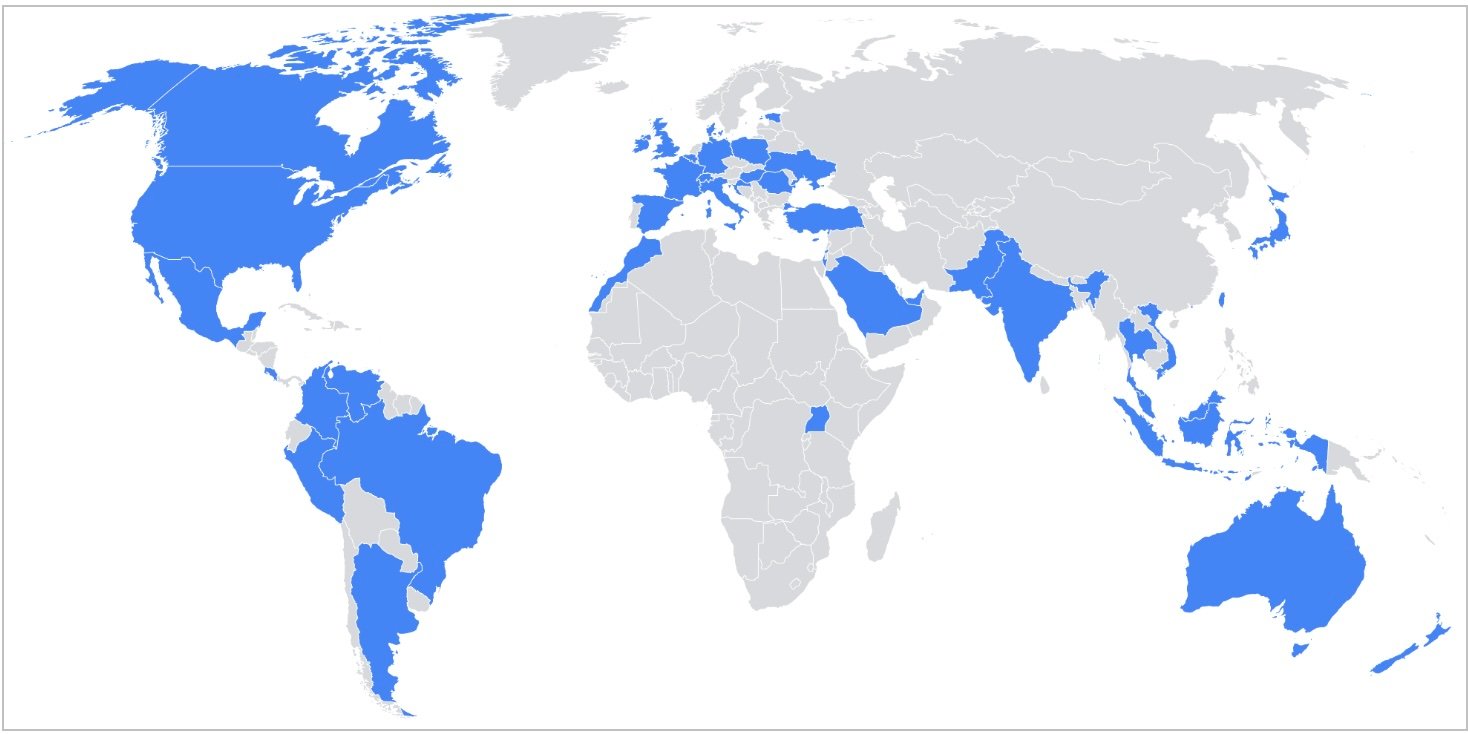
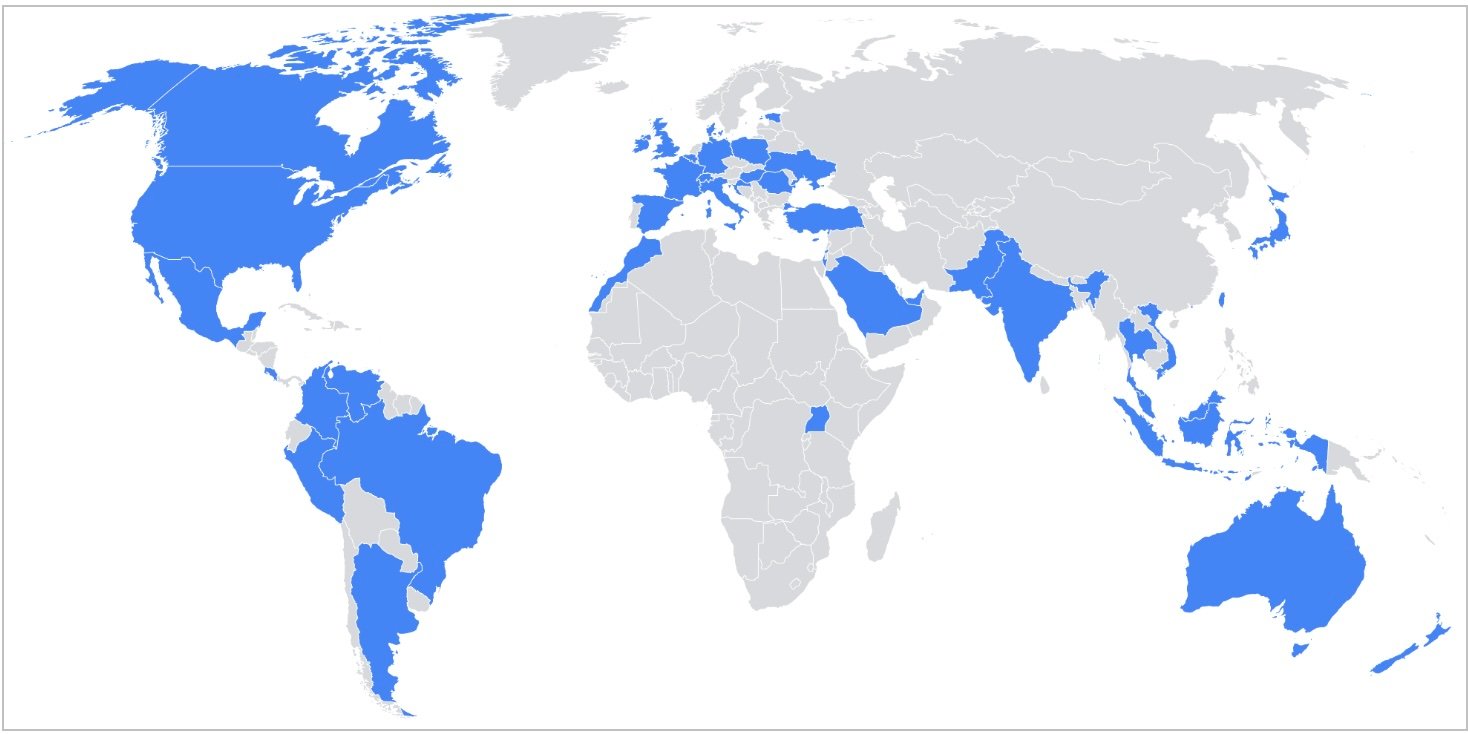
Strategic Expansion in Europe
Following severe sanctions and legal challenges in the United States, North Korea’s IT workforce has pivoted towards European markets, particularly targeting corporate entities in Germany, Portugal, and the United Kingdom. This expansion aims to generate significant revenue for the Democratic People’s Republic of Korea (DPRK).
Tactics of Deception
The operatives employ sophisticated strategies to mask their true identities. Representing themselves from diverse nationalities, such as Italian, Japanese, and American, these DPRK IT workers deftly manipulate professional environments:
- Usage of complex fabricated and stolen identities.
- Employment obtained through popular online platforms like Upwork and Telegram.
- Remuneration routed through cryptic channels including cryptocurrencies and digital payment platforms to obscure financial trails.
Scope of Infiltration
Security investigations reveal that DPRK IT impersonators have infiltrated numerous sectors including:
- Advanced technologies such as AI and blockchain.
- Web, bot, and CMS development projects in the UK.
- Defense and governmental bodies across Europe, using forged documents and fake references.
U.S. Response to DPRK IT Offensives
The United States has stepped up its countermeasures against North Korea’s overseas IT operations which include:
- Federal indictments and sanctions against individuals and companies involved in the DPRK’s IT schemes.
- Continued efforts by the U.S. Treasury to disrupt these operations financially.
- Extensive collaboration with international bodies to entrap and eliminate DPRK’s IT infiltration.
Implications and Future Threats
The persistent and evolving threat from DPRK’s IT workforce not only endangers corporate security but also poses a significant challenge to global cybersecurity. Awareness and stringent security measures are essential to safeguard sensitive information and protect organizational integrity.
Related: Unveiling the Intricacies of a Sophisticated Malware Delivery Chain: A Detailed Breakdown
Last Updated: April 1, 2025




