
Overview of Fast Flux DNS
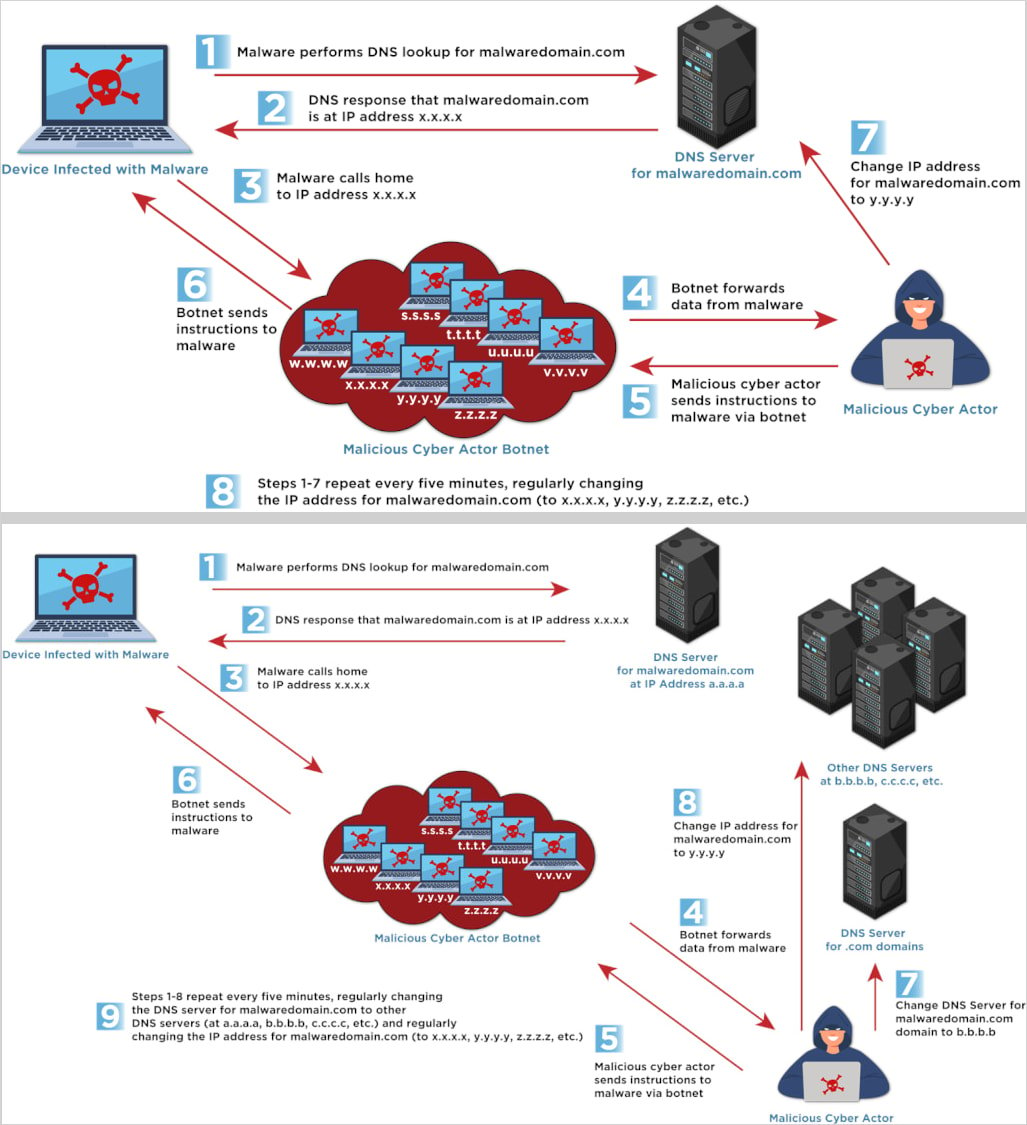
Fast Flux DNS is a complex DNS technique utilized for evasion, maintaining resilient infrastructures for malicious operations such as command and control (C2), phishing, and malware dissemination. This method involves swiftly altering DNS records, including IP addresses and name servers, which complicates the efforts of cybersecurity defenders to locate and neutralize the threat sources.
Understanding the Technique
The method leverages botnets – large networks of compromised systems acting as proxies – to execute rapid DNS changes. This makes it extremely difficult for cybersecurity measures to trace and mitigate the malicious activities.
According to CISA’s advisory, there are two primary variations of this technique:
- Single Flux: IP addresses linked with a domain name are rotated frequently.
- Double Flux: Both IPs and DNS name servers are rotated, adding an extra layer of difficulty for tracking and takedown.
This technique is favored by a wide spectrum of threat actors, ranging from individual cybercriminals to sophisticated nation-state entities, for its efficacy in evading detection.
Highlighted Threats and Case Studies
Fast Flux has been effectively employed by various notorious groups. CISA cites cases involving Gamaredon, Hive ransomware, Nefilim ransomware, and even some bulletproof hosting services, utilizing Fast Flux to dodge law enforcement and disrupt takedown operations.
Proactive Measures and Recommendations by CISA
CISA has proposed several detection and mitigation strategies to counter the threats posed by Fast Flux networks:
Detection Strategies
- Analyze DNS logs for signs like frequent IP changes, short TTL values, high IP entropy, and geographically inconsistent resolutions.
- Integrate threat intelligence feeds and DNS/IP reputation services within security architectures to identify and manage known Fast Flux domains.
- Monitor network flows and DNS traffic to spot excessive queries or connections to various IPs in abbreviated times.
- Scrutinize for suspicious domains or emails that could be part of a Fast Flux-supported phishing or malware campaign.
- Implement tailored detection algorithms focused on your historical DNS activity and network behavior to improve specificity and reduce false positives.
Mitigation Techniques
For effective risk mitigation, incorporate DNS/IP blocklists, apply firewall rules to restrict access to identified Fast Flux infrastructures, and possibly redirect traffic for deeper analysis. Reputational scoring, centralized logging, real-time alerts for DNS anomalies, and participating in threat-sharing networks are also critical to strengthen defenses against such evasion techniques.
Embrace these expert strategies to safeguard your digital frontiers against Fast Flux DNS threats and ensure robust cyber resilience.
Related: Essential Update: Ivanti Releases Patches for Critical Connect Secure Vulnerability
Last Updated: April 3, 2025