Introduction
Penetration testing, commonly referred to as ethical hacking, plays a pivotal role in cybersecurity. It involves the proactive identification and exploitation of security vulnerabilities in network systems and software applications. A wide array of robust tools is available to assist cybersecurity professionals in this task, each designed to target specific areas of a security framework.
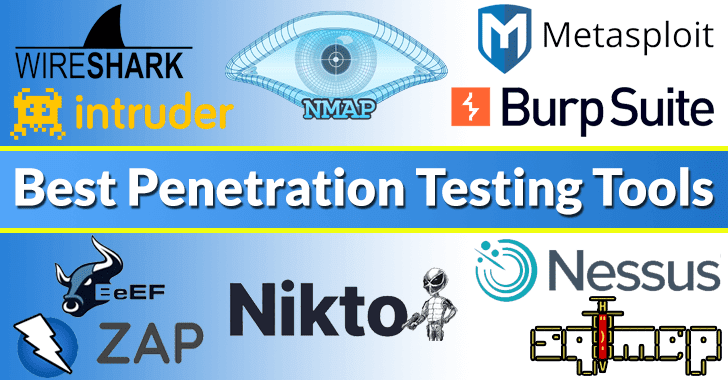
Top Penetration Testing Tools
The selection of a penetration testing tool can depend on a multitude of factors including the specific security requirements of the system, the complexity of the network, and the tester’s expertise. Here’s a breakdown of the top tools used in the industry:
- Metasploit: Known for its extensive database of exploits, Metasploit facilitates complex and comprehensive tests.
- Wireshark: This network protocol analyzer helps in capturing and making sense of network traffic.
- Nmap: Nmap excels in network mapping to discover devices and services.
- Burp Suite: Highly favored for web application testing, it includes tools for mapping out and analyzing application attack surfaces.
- SQLmap: Specializes in automating the detection of SQL injection flaws in database-driven applications.
Diving Deep into Featured Tools
Let’s explore more details about some of the prominent tools:
1. Metasploit
Metasploit is popular for providing information about security vulnerabilities and aids in IDS signature development. Its comprehensive framework can be used to build security tools and execute penetration tests.
2. Wireshark
Wireshark offers features that capture packets in real-time and display them in human-readable format for easy identification of network issues.
3. Nmap
Used mainly for network discovery and security auditing, Nmap’s flexible command line interface allows deep customization and detailed results.
4. Burp Suite
With its intuitive user interface, Burp Suite is effective for testing the security of web-based applications, performing manual and automated tests.
5. SQLmap
SQLmap automates the process of detecting and exploiting SQL injection vulnerabilities in an application’s database. It supports multiple database systems and can perform password hash recognition and dictionary attacks.
Conclusion
Choosing the right tool is about understanding the specific needs of your IT environment. Employing a combination of these tools can significantly enhance an organization’s cybersecurity measures, preparing it to better withstand malicious cyber threats.
Explore more about each tool »
Related: Check Point Acknowledges Data Breach, Claims Information is ‘Old
Last Updated: April 1, 2025