Overview of the Recent Cybersecurity Threat
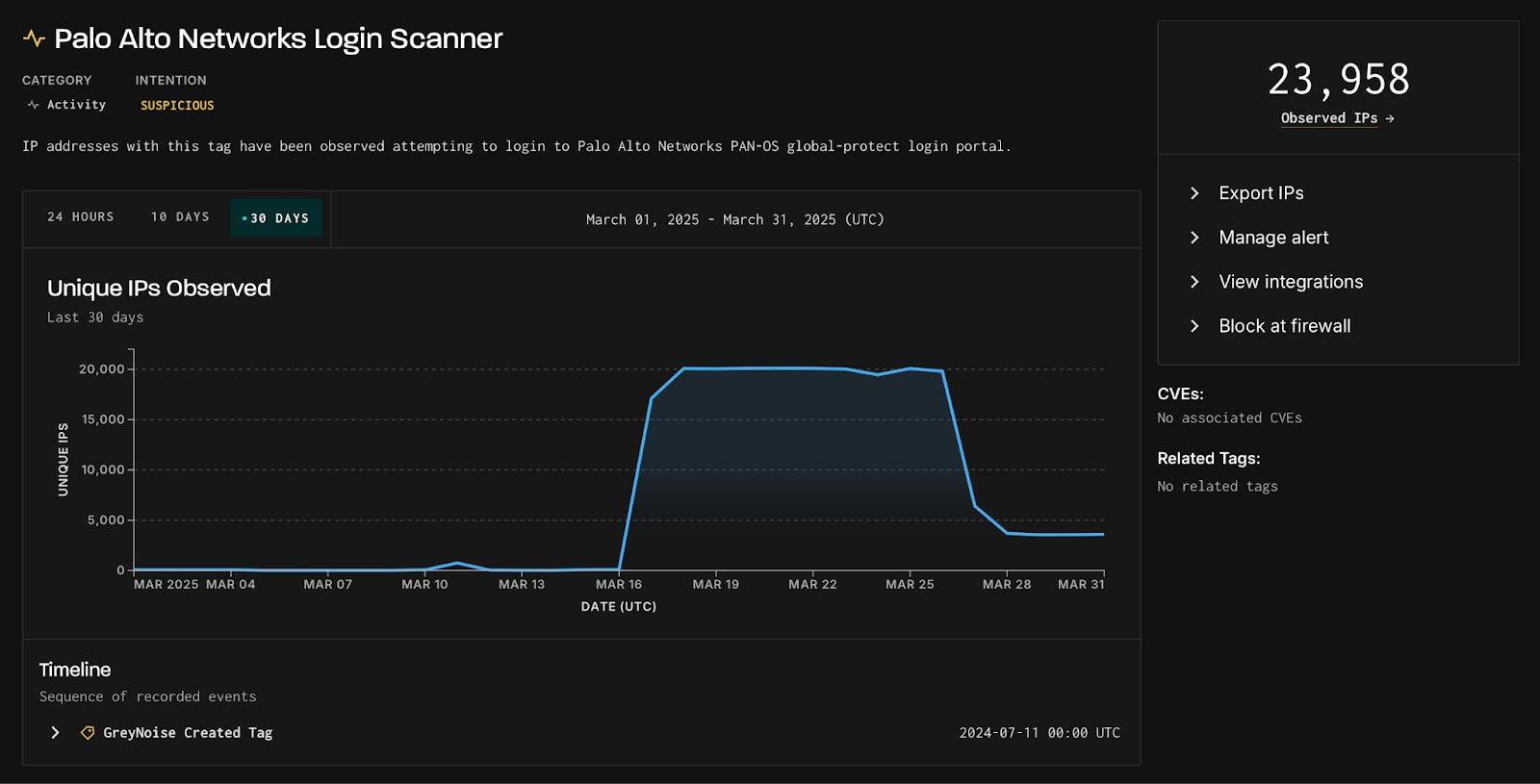
A sharp increase in scanning activities aimed at Palo Alto Network GlobalProtect login portals has raised alarms about a potential looming attack or exploitation of vulnerabilities.
Key Details from GreyNoise
The threat monitoring entity GreyNoise has observed this notable surge involving more than 24,000 unique IP sources. The scanning activities reached their peak on March 17, 2025, with 20,000 IPs being active on that day alone, and continued aggressively till March 26.
- Out of the observed IPs, 23,800 are deemed ‘suspicious’
- A smaller fraction, 154 IPs, have been confirmed as ‘malicious’
Majority of these attempts originated from the United States and Canada, directly targeting systems predominantly within the U.S., amongst others globally.
Visual Data on Scanning Activity
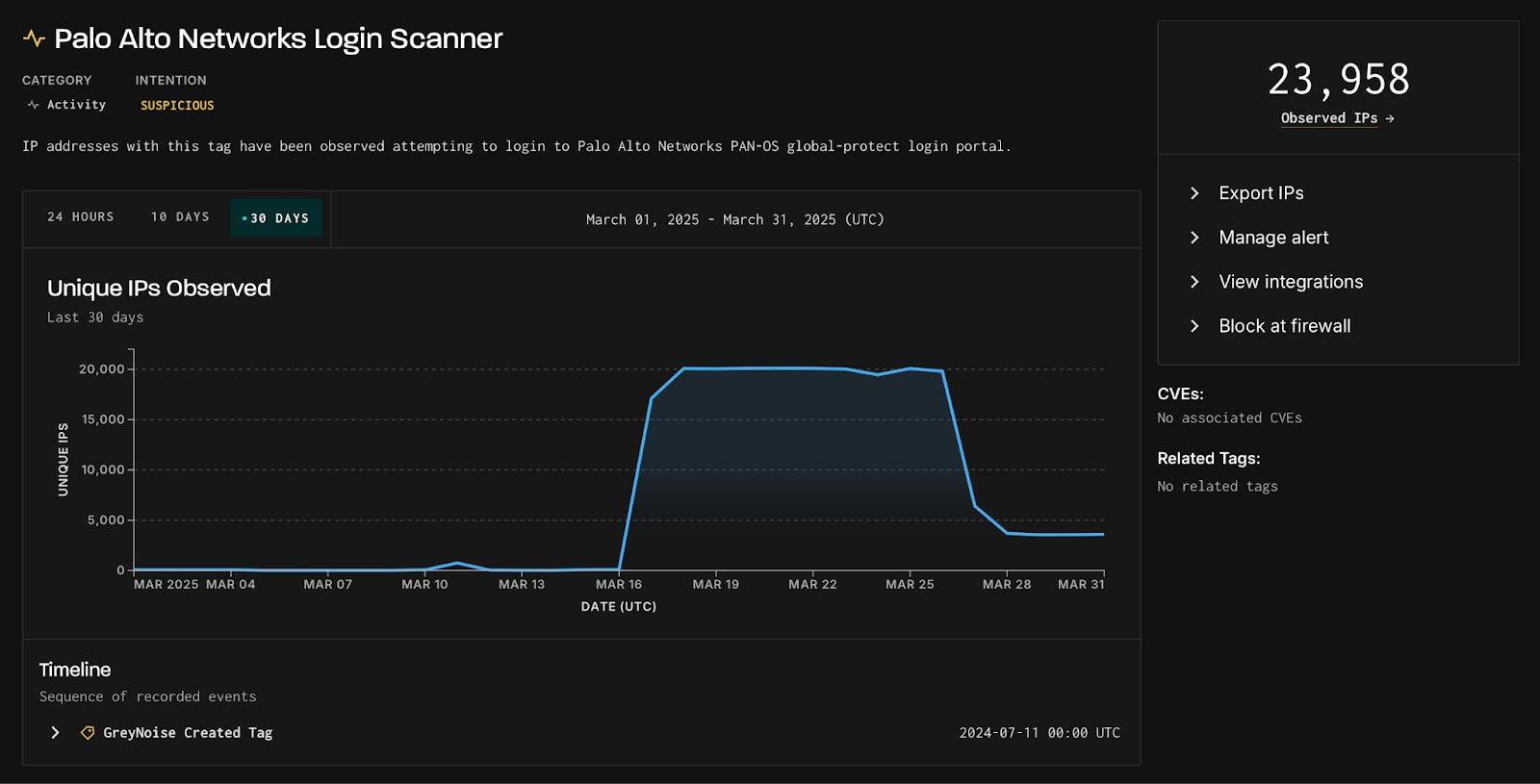
Courtesy of GreyNoise
Understanding the Implications
Historically, similar spikes in network scanning activity serve as a precursor to the revelation of significant security flaws. Often, the peaks are followed by vulnerability disclosures within two to four weeks. GreyNoise’s analysis suggests a strategic pattern targeting existing vulnerabilities and possible reconnaissance efforts aimed at particular technologies.
Connections to Previous Cyber-Espionage
On a paralleled note, there is an observed spike in activities from a PAN-OS crawler which occurred concurrently on March 26, involving 2,580 IPs. This behavior aligns with past espionage campaigns like those attributed to the ‘ArcaneDoor’ by Cisco Talos, primarily targeting edge devices.
Recommended Actions
With the landscape of threat activity currently ambiguous but potentially serious, GreyNoise advises administrators of internet-exposed Palo Alto Networks systems to elevate their security measures:
- Review security logs from mid-March onwards to identify any targeted activities
- Survey for possible signs of compromise
- Enhance the security of login portals
- Block IPs identified as malicious in the report
BleepingComputer has reached out to Palo Alto Networks for further comments regarding the observed activities and will provide updates as new information becomes available.
Related: Essential Security Updates: Apple Enhances Protection for Older iPhones and Macs with
Last Updated: April 1, 2025